


Monitoring, Auditing and Reporting in BPO Security
How Felcorp monitors activity, maintains audit trails and provides reporting to support security oversight and incident response.
Last updated
March 13, 2026
Felcorp monitors all access, activity and engagement delivery across the platform on an ongoing basis. This monitoring serves both security and operational purposes: identifying any unusual activity that might indicate a risk, and providing management with visibility over how services are being delivered and how effectively security controls are functioning.
This monitoring generates a comprehensive audit trail that can be reviewed by Felcorp management and provided to clients where required.
Activity Monitoring
All access to client data, including who accessed it, when it was accessed and what was done with it, is recorded automatically. This includes:
- System activity on Felcorp devices and servers
- Credential access and usage
- Endpoint protection alerts and threat detections
- Network traffic and connection logs
- Email delivery and security filtering events
These logs are retained and can be searched, reviewed and analysed to investigate any suspicious activity, to verify data handling compliance or to establish a complete record of engagement activity.
Performance Reviews
Division Managers review task completion, timesheet submissions and work quality on a daily and weekly basis. This provides direct oversight of operational activity and helps identify where process improvements or additional training might be needed.
Performance is also assessed through mid-year and annual reviews, which evaluate adherence to data handling procedures, compliance with confidentiality obligations and overall competency development.
Security Event Monitoring
Threat detection systems across Felcorp's infrastructure monitor for suspicious activity including malware, unusual network connections, brute-force attempts or other signs of compromise. Where a potential security event is detected, alerts are generated for immediate investigation.
Felcorp management has the ability to remotely access and respond to any device or user account suspected of suspicious activity, take corrective measures and escalate incidents where necessary.
Audit Trail and Investigation
Where an incident occurs or an investigation is required, Felcorp's centralised audit systems provide a complete record of who did what and when. This includes:
- A timeline of all user access and activity
- Email delivery and communication logs
- File transfers and data movement
- System administration changes
- Endpoint activity and threat events
This audit trail supports post-incident analysis, compliance reporting and any investigation required by law enforcement or regulatory bodies.
Reporting to Clients
Felcorp can provide reporting to clients on request, including:
- Confirmation that their data has been handled according to agreed procedures
- Access logs showing which staff members accessed their data and when
- Summaries of any security events or unusual activity
- Proof of data deletion or transfer when an engagement concludes
Reporting frequency and content can be configured to match client requirements and regulatory obligations.
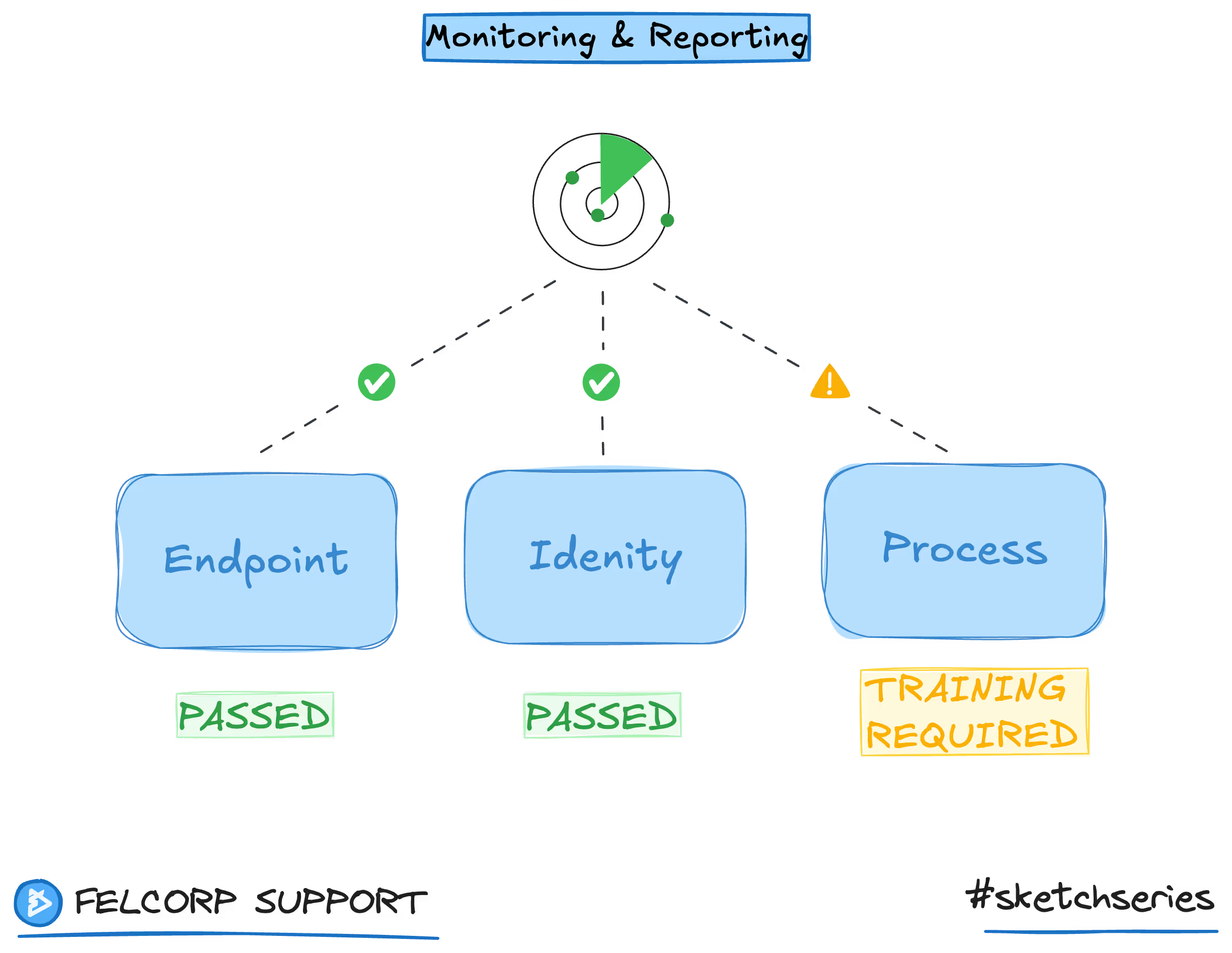
How This Fits the Security Framework
Monitoring and reporting sit at the intersection of all three layers in Felcorp's security framework. Design-level controls like encryption and firewalls are monitored for effectiveness. Operational procedures are reviewed to ensure compliance. Engagement-level separation is verified through access logs and audit trails.
Together, monitoring and reporting provide the visibility needed to confirm that security controls are working as intended and to detect and respond to any breaches or suspicious activity.
On this page
