


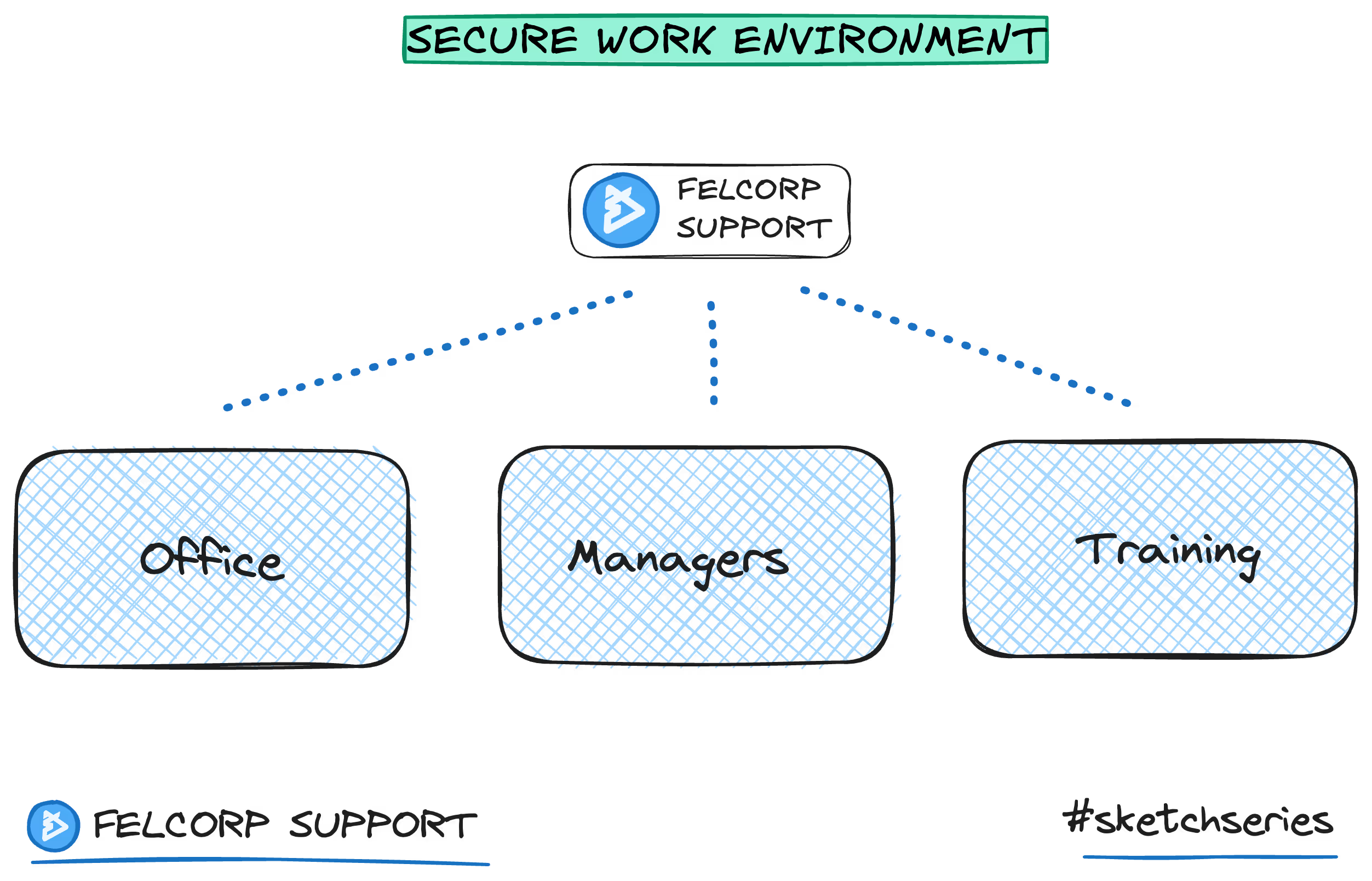
Secure Working Environments in BPO Operations
How Felcorp's onsite work environment, physical access controls and management oversight protect client data from disclosure.
Last updated
March 9, 2026
"Secure" is one of those words that gets thrown around in every BPO proposal. Every provider claims to be secure. But what does security actually mean? What should your secure working environment actually look like?
Secure BPO working environments protect confidentiality by maintaining controlled operations across physical locations and access controls.
Real security is boring. It's not about drama or high-tech wizardry. It's about systems and controls that prevent bad things from happening.
Physical security
Your offshore team needs a secure physical environment. This means:
Controlled access to the office. Visitors should require approval. Employees should have access badges.
Cameras. Office areas should have surveillance cameras. This deters theft and creates a record if something happens.
Secure storage. Sensitive documents should be locked up when not in use. Computers should be in a secure location, not accessible to visitors.
Clean desk policy. When not using sensitive materials, they should be locked away. This prevents casual observation by people walking by.
These aren't sexy, but they work. A locked drawer prevents accidental data leaks far more effectively than any technology.
System security
Your offshore team needs secure systems to work with. This means:
Encrypted connections. Data in transit should be encrypted. VPNs, HTTPS, and TLS should be standard.
System access controls. Staff should only have access to systems they need for their job. Access should be logged and monitored.
Antivirus and antimalware. Systems should have protection against viruses and malware. Definitions should be current.
Firewalls. Network traffic should be filtered. Unauthorized traffic should be blocked.
These controls are table stakes. Your provider should have all of these. If they don't, that's a red flag.
Data security
Data in the provider's custody should be protected:
Data at rest should be encrypted. If a hard drive is stolen, it's useless without the encryption key.
Data in transit should be encrypted. Data between your systems and the provider's systems should be encrypted.
Data access should be logged. Who accessed what data, when, and why should be recorded.
Data deletion should be documented. When data is no longer needed, it should be securely deleted. There should be evidence that deletion happened.
Network security
The provider's network should be secure:
Network segmentation. Work systems should be separated from the provider's other business systems. Your data shouldn't be accessible from general purpose networks.
Intrusion detection. The network should monitor for suspicious activity. Unauthorized access attempts should be detected and blocked.
Penetration testing. The network should be regularly tested for vulnerabilities. Weaknesses should be fixed before they can be exploited.
Vulnerability scanning. Systems should be scanned regularly for known vulnerabilities. Updates should be applied promptly.
Access control
Who can access your data should be tightly controlled:
Principle of least privilege. Staff should have only the minimum access needed to do their job.
Multi-factor authentication. Logging in should require more than just a password. Use two-factor authentication for sensitive systems.
Access logging. Every access to sensitive data should be logged. Later, you should be able to see who accessed what.
Access revocation. When staff leave, their access should be immediately revoked. Former employees shouldn't be able to access your data.
Personnel security
Your provider's staff should be vetted:
Background checks. Staff handling sensitive data should have background checks. These should match your risk tolerance.
Confidentiality agreements. Staff should sign agreements acknowledging their responsibility to protect confidential data.
Training. Staff should receive security training. They should understand data handling procedures and social engineering risks.
References. Check the staff member's references and work history. Verify they're who they claim to be.
Third-party management
Your provider shouldn't be the only party with access to sensitive data:
Vendor vetting. If your provider uses third-party tools or services, those vendors should also be vetted for security.
Data processing agreements. Any third party processing your data should have a data processing agreement that includes security requirements.
Right to audit. Your contract should include the right to audit your provider's security practices and those of their vendors.
Incident management
Bad things sometimes happen. Your provider should have incident response procedures:
Incident detection. The provider should have systems in place to detect security incidents.
Incident response. When an incident is detected, there should be a defined process to contain it and remediate it.
Notification. You should be notified of incidents that affect your data promptly. There should be defined timeframes for notification.
Investigation. The provider should investigate incidents to determine what happened and how to prevent recurrence.
Compliance certifications
Look for providers with relevant compliance certifications:
ISO 27001. This is an information security management system certification. Providers with ISO 27001 have had their security practices independently audited.
SOC 2. This is a security, availability, and confidentiality audit. It verifies the provider has adequate controls.
HITRUST. This is specifically for healthcare data. Providers with HITRUST are compliant with HIPAA and other healthcare privacy regulations.
Industry-specific certifications. If you're in a regulated industry, look for certifications specific to your industry.
Contractual protections
Your contract should include security requirements:
Security standards. The contract should specify what security controls your provider must maintain.
Audit rights. You should have the right to audit the provider's security practices.
Breach notification. The contract should specify how quickly you'll be notified of breaches.
Compliance requirements. The contract should specify what compliance requirements your provider must meet.
Indemnification. The contract should specify liability if your provider's security failure causes you harm.
The bottom line
Secure BPO working environments require controls across physical security, system security, network security, access control, personnel security, and incident response. Look for providers with ISO 27001 or SOC 2 certification. Verify they have the specific controls you need for your data. Test their security in your due diligence process. Don't just trust their claims. Ask for evidence.
On this page
