


Technology and Endpoint Security in BPO Operations
How Felcorp secures devices, networks and endpoints to protect client data across outsourced financial services engagements.
Last updated
March 7, 2026
Every device used in a Felcorp engagement is company-owned, centrally managed and configured to enforce security controls before any client work begins. Personal devices are not permitted to access client data, systems or networks under any circumstances.
This approach ensures Felcorp maintains full visibility and control over every endpoint involved in service delivery.
Device Configuration and Lockdown
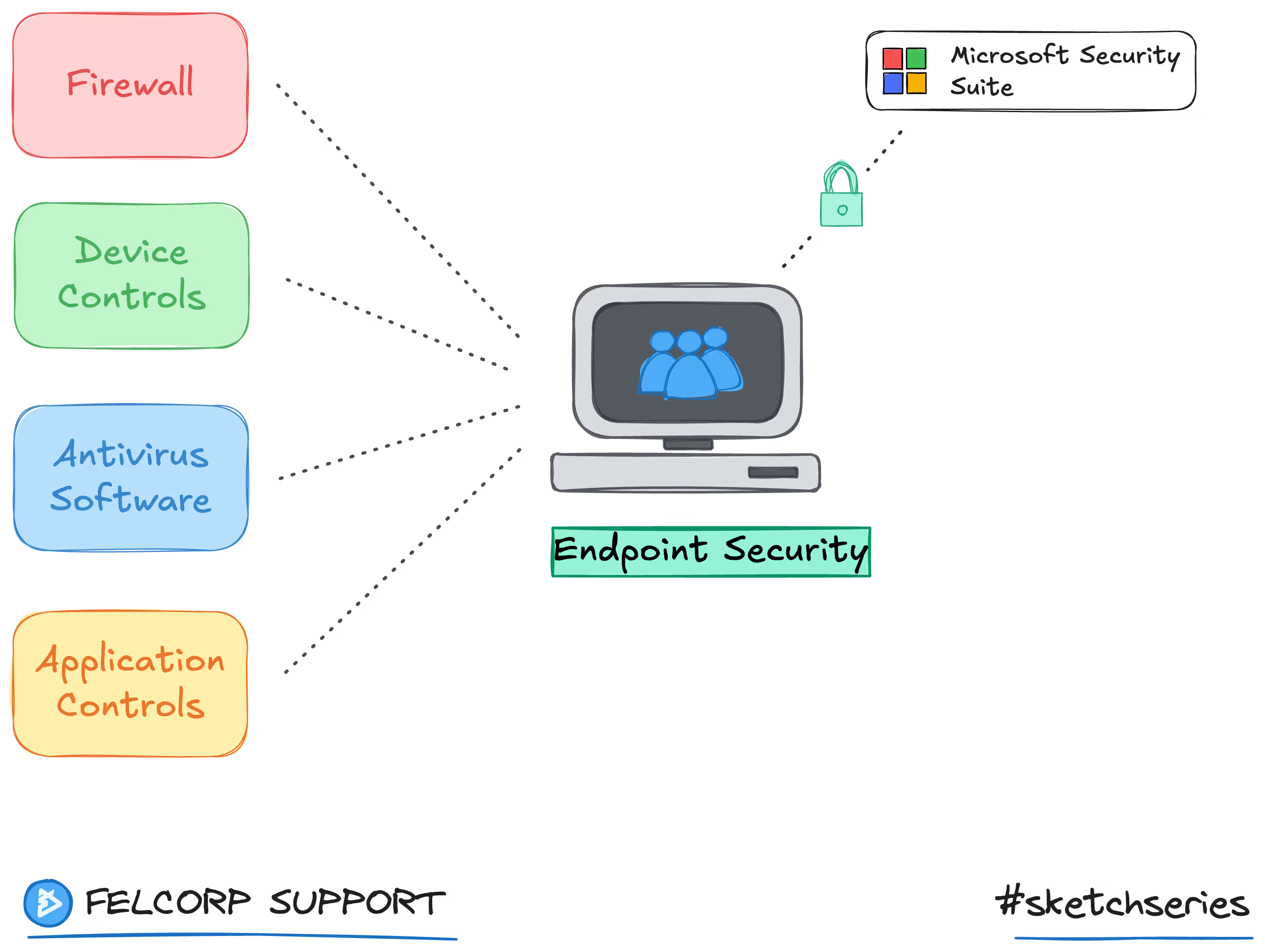
All workstations operate within a centrally managed IT tenant environment. Each device is enrolled and governed through this platform, which enforces firewalls, device controls, antivirus software and application controls at the endpoint level before any client work begins.
Staff cannot install software, modify system settings or bypass security configurations. All device policies are enforced centrally and cannot be overridden at the local level. Felcorp management has the ability to enforce specific IT policies remotely, including approved internet connections, website blacklisting and peripheral restrictions such as disabled USB and external storage ports.
Endpoint Protection
Every device runs an enterprise endpoint protection platform with real-time threat detection, anti-malware scanning and behavioural analysis. Protection agents are centrally deployed and monitored, with automatic updates applied without relying on user action.
The platform provides end-to-end encryption and protection across all internal and external information ports, automatically scanning new data for threats. All internet access on Felcorp devices is routed through a secure VPN connection built into the endpoint protection suite.
Felcorp management receives alerts and can remotely access devices in response to suspicious activity, unauthorised software or potential security threats. A comprehensive audit log records all endpoint activity for review.
Email Security
Felcorp enforces a multi-layered email security framework to reduce phishing, spoofing and interception risks. This includes domain-level authentication protocols that verify sender identity and prevent impersonation, encryption of email traffic between mail servers and monitoring against known threat intelligence databases.
All outgoing and incoming email is transmitted over encrypted connections. Felcorp's domain is verified as clean across threat intelligence databases with no history of spam, phishing or low reputation activity.
Network Security
All network traffic between Felcorp's environment and client systems is encrypted in transit. Staff connect through secured network infrastructure with firewall controls, intrusion detection and traffic filtering applied at the perimeter.
Remote access is only permitted through approved secure channels with multi-factor authentication enforced at the connection level. Direct internet access from production workstations is restricted and routed through monitored gateways.
Application and Access Controls
Only approved applications are permitted to run on Felcorp devices. Application whitelisting prevents the execution of unauthorised software, reducing the risk of data exfiltration tools or unapproved communication channels operating on production endpoints.
Web access is filtered to block high-risk categories and prevent access to file-sharing, personal email and social media platforms from production workstations.
Credentials are managed through an enterprise password management platform with centralised audit controls. Passwords are never shared directly between staff. Management retains full visibility over credential access and usage across all client engagements.
Document and Data Storage
Client information is stored exclusively within Felcorp's approved file management platform, accessible to the client in full transparency. No client data is held on local desktops, personal storage or unapproved cloud services.
Internal operational information is managed separately from client data. All data is protected during transmission and at rest through encryption and access controls described in Felcorp's Operational Processes and Policies.
Patching and Updates
Operating systems and applications are patched on a regular cycle managed centrally by Felcorp's IT team. Critical security patches are prioritised and applied within defined timeframes to reduce exposure to known vulnerabilities.
Patch compliance is tracked and reported as part of ongoing Monitoring and Reporting activities.
Personal Device Restrictions
Access to work accounts from personal devices such as mobile phones, tablets or laptops is restricted to the office environment and work hours only. All personal device access must be performed through verified Felcorp network connections.
Employees are required to keep device passwords secure, shut down screens when away from their desk and ensure antivirus software is kept current.
How This Fits the Security Framework
Technology and endpoint security sits within the Security By Design layer of Felcorp's three-layer framework. These controls are established at the platform level and apply to every engagement before any client-specific configuration is added.
For detail on how user access is managed on top of these device controls, refer to Identity and Access Management.
On this page
