


Our Security and Risk Philosophy for BPO Services
How Felcorp embeds security across design, operations and client engagements to protect data in outsourced financial services.
Last updated
March 7, 2026
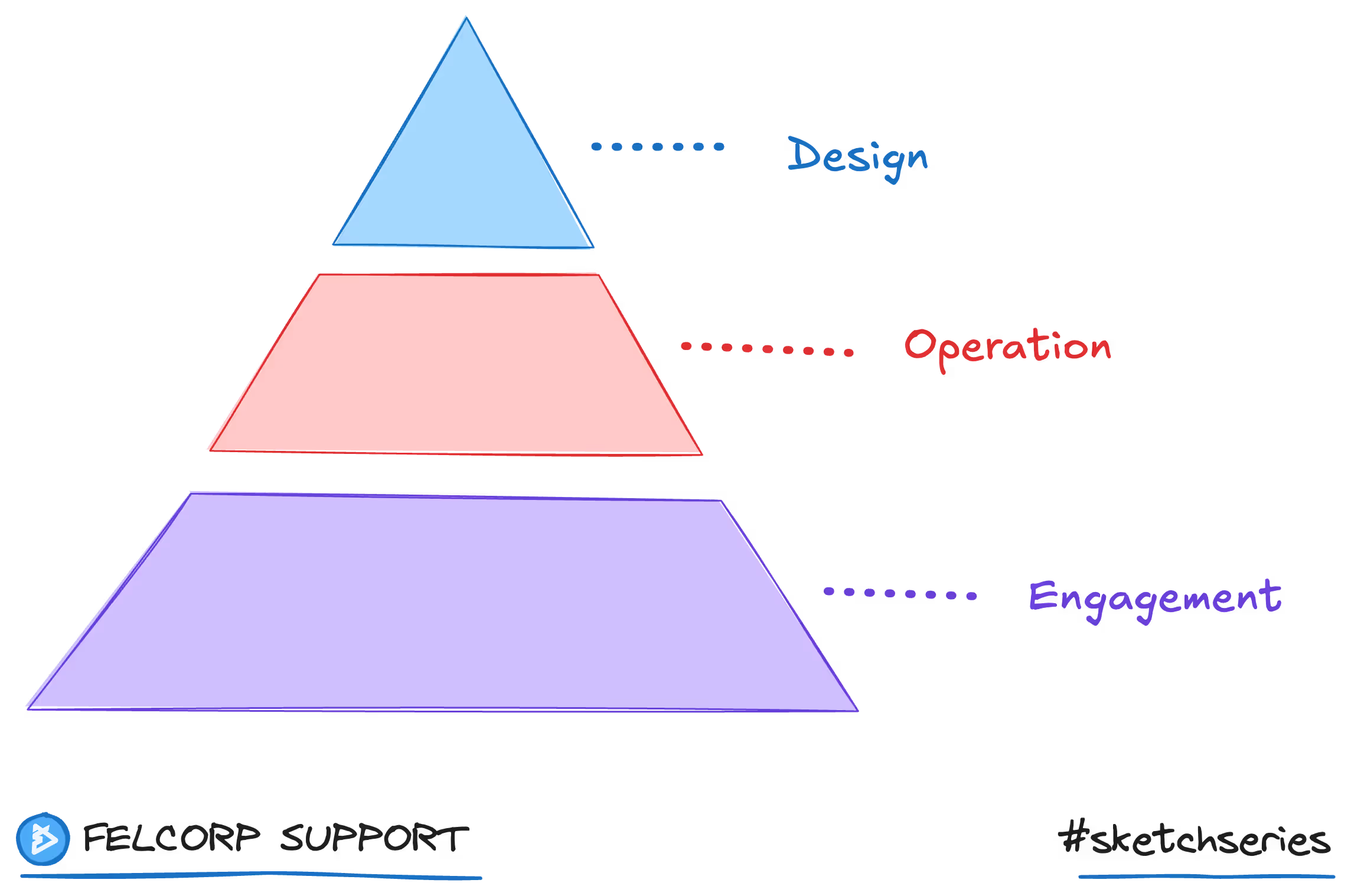
Felcorp's approach to security is built on the principle that protection must exist at every level of the service, not as an afterthought or a single policy applied uniformly. Security in outsourced financial services requires layered controls that address risk at the structural, operational and engagement level.
This philosophy is reflected in a three-layer framework that governs how security is designed, deployed and maintained across all Felcorp engagements.
Security By Design
Security by design means protections are embedded into the architecture of how Felcorp's BPO solution is built and governed from the outset. This includes the physical environment, network infrastructure, endpoint configuration and access management systems that underpin every engagement.
These controls exist before any client data enters the environment. They are not reactive measures added in response to incidents. They are structural decisions made at the platform level to ensure the foundation is secure by default.
For detail on how these controls work in practice, refer to Technology and Endpoint Security and Identity and Access Management.
Security By Operation
Each BPO operation serves a specific industry vertical with its own risk profile. Financial planning, accounting and insurance each carry different regulatory obligations, data sensitivity levels and workflow requirements.
Security by operation means Felcorp deploys targeted security policies to each service area based on the risks relevant to that industry. A financial planning operation handling client portfolio data is governed differently from an accounting operation processing tax lodgements.
This layer ensures controls are proportionate and relevant rather than generic. For detail on how operational security policies are structured, refer to Operational Processes and Policies.
Security By Engagement
The most granular layer of protection is applied at the individual client engagement level. Each engagement is configured with its own access controls, data separation rules and confidentiality obligations specific to that client's requirements.
This means information belonging to one client is never visible to staff working on another engagement. Access is provisioned per engagement, monitored throughout and revoked at off-boarding.
For detail on engagement-level protections, refer to Client and Engagement-Level Separation and Non-Disclosure Agreements.
How the Three Layers Work Together
A secure endpoint is ineffective if operational processes allow data to be mishandled. Strong operational policies are undermined if engagement-level separation is not enforced.
The three layers are designed to reinforce each other. Design-level controls create the secure foundation. Operational controls tailor protections to industry-specific risk. Engagement-level controls ensure every individual client relationship is protected on its own terms.
Continuous Improvement
Felcorp reviews and updates security controls on an ongoing basis in response to changes in technology, regulation and the threat landscape. This includes regular internal audits, monitoring and reporting across all three layers.
For detail on how Felcorp monitors and responds to security events, refer to Monitoring and Reporting.
On this page
