Enterprise-Grade Security Built Into Every BPO Engagement
Protecting client data, maintaining confidentiality and meeting regulatory expectations across financial services.

Our 3 pillar security framework
Securing technology environments, controlling access priviledges and ensuring information is handled safely throughout its lifecycle.
Enforcing strict confidentiality obligations across teams and processes ensuring what belongs to your firm and your clients remains private at all times.
Ensuring ongoing alignment with legal, regulatory and governance requirements to enable financial services firms to outsource with confidence.
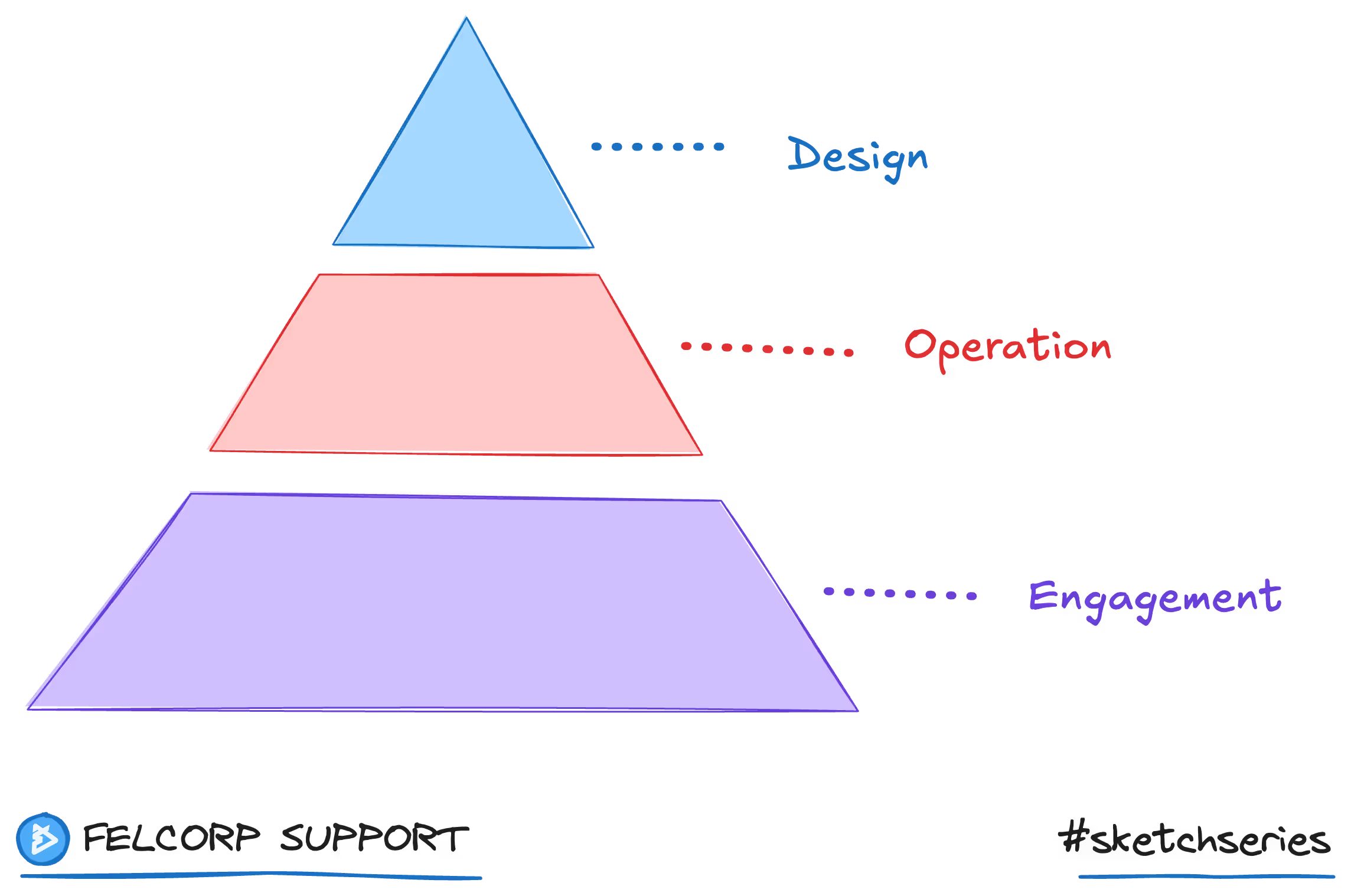
Our Security Philosophy
Security By Design
Security is embedded into how our BPO solution is designed, governed and controlled from the outset.
Security By Operation
Specific security policies are deployed to each BPO operation to protect against targeted industry risks.
Security By Engagement
Specific security policies are deployed for each individual client engagement to better protect and mitigate risk.
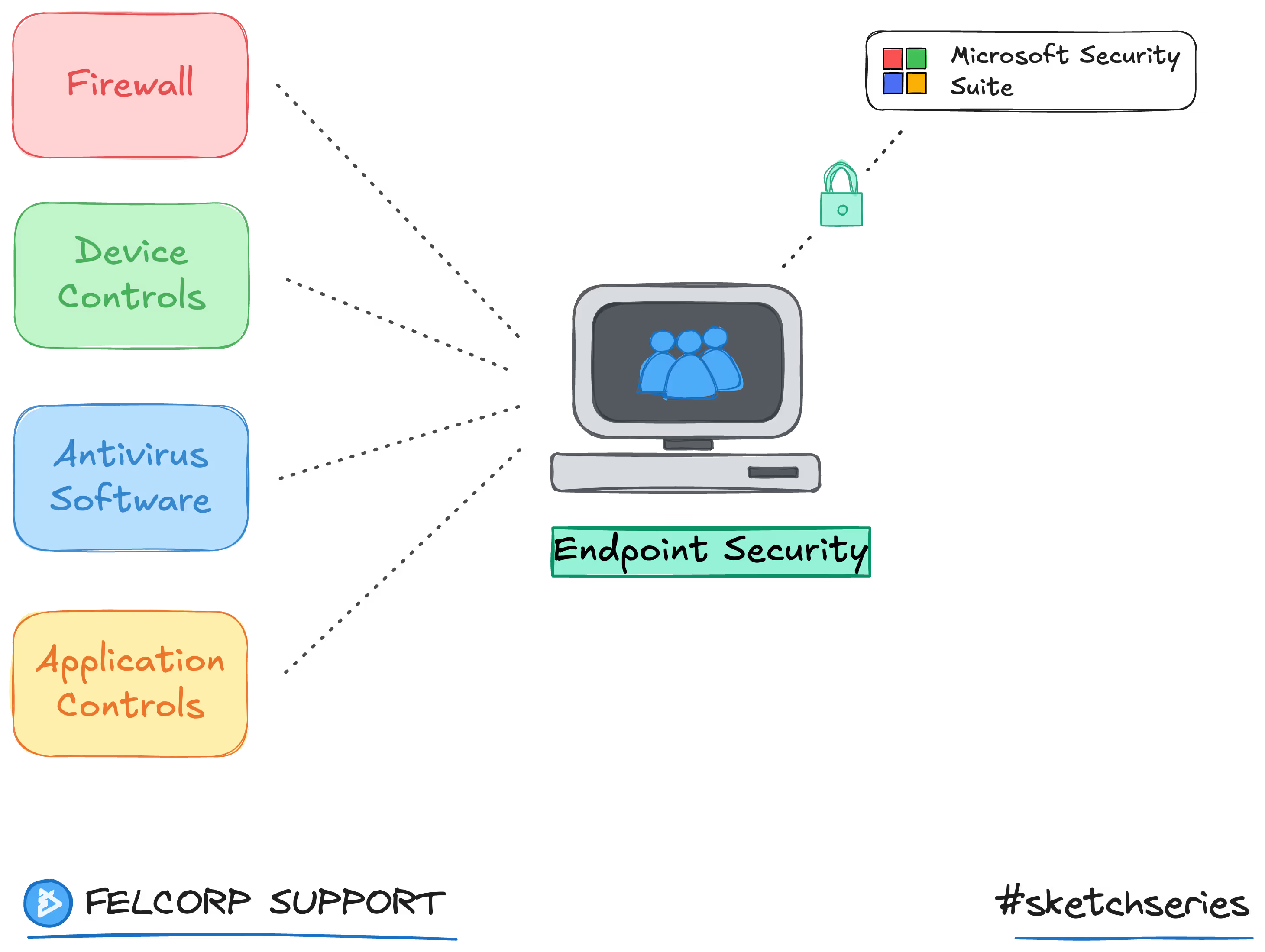
Technology and Endpoint Security
Devices are locked down, continuously protected to prevent unauthorised access and malware intrusions. Security controls are enforced at the endpoint level to ensure data is protected where work is performed.
Identity and Access Management
Identity and access management ensures only authorised users can access systems and data. Access is role-based and removed promptly when responsibilities change.
Operational Processes and Policies
Ensuring data is handled consistently and securely across all workflow activities. Defined workflows, approvals and training embed security into day-to-day operations to reduce poor data handling behaviour.
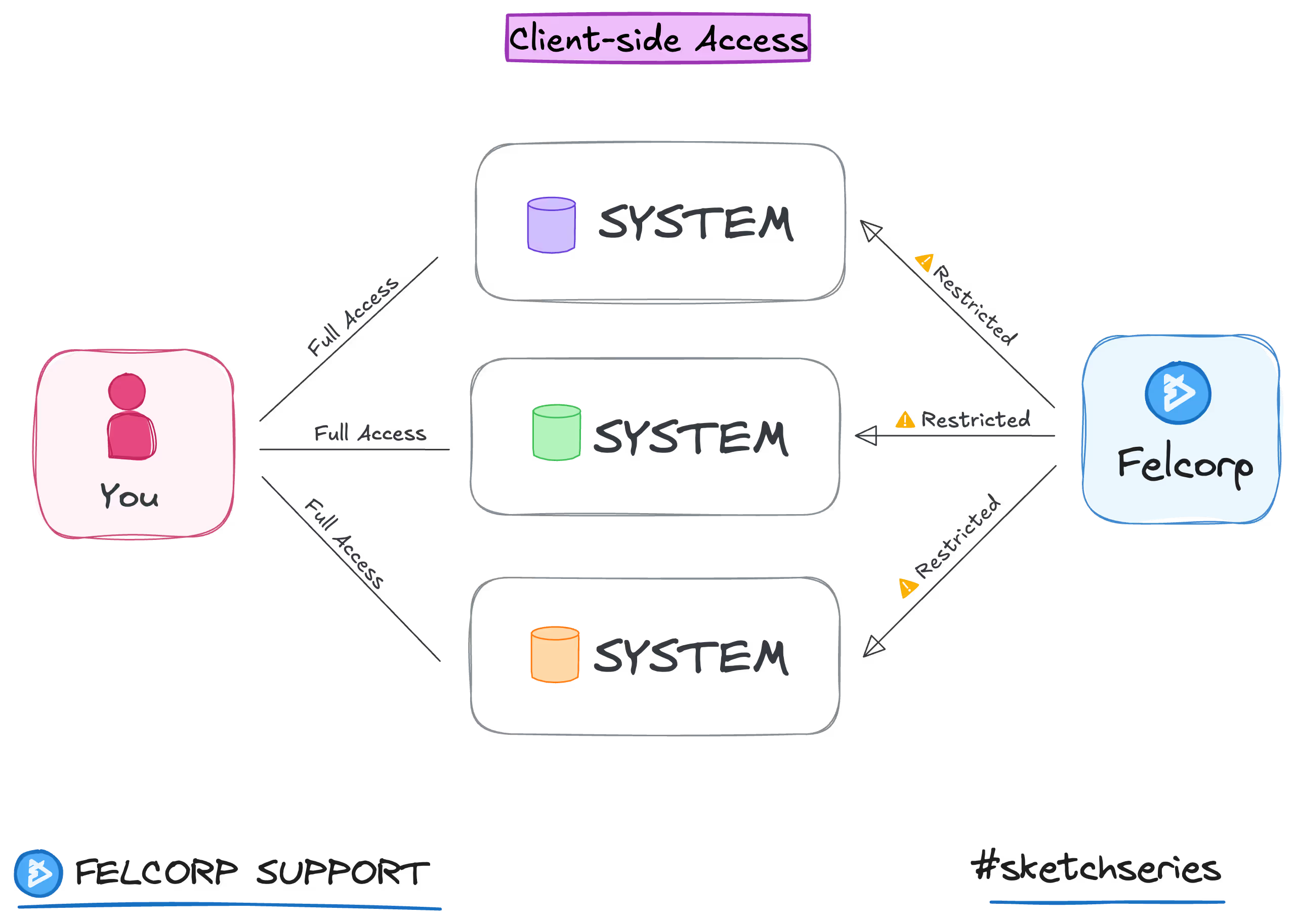
Client-Side System Access
Security protocols for team access to client systems as required to facilitate work. Permissions are set at the client end with correct role and data access priviledges.
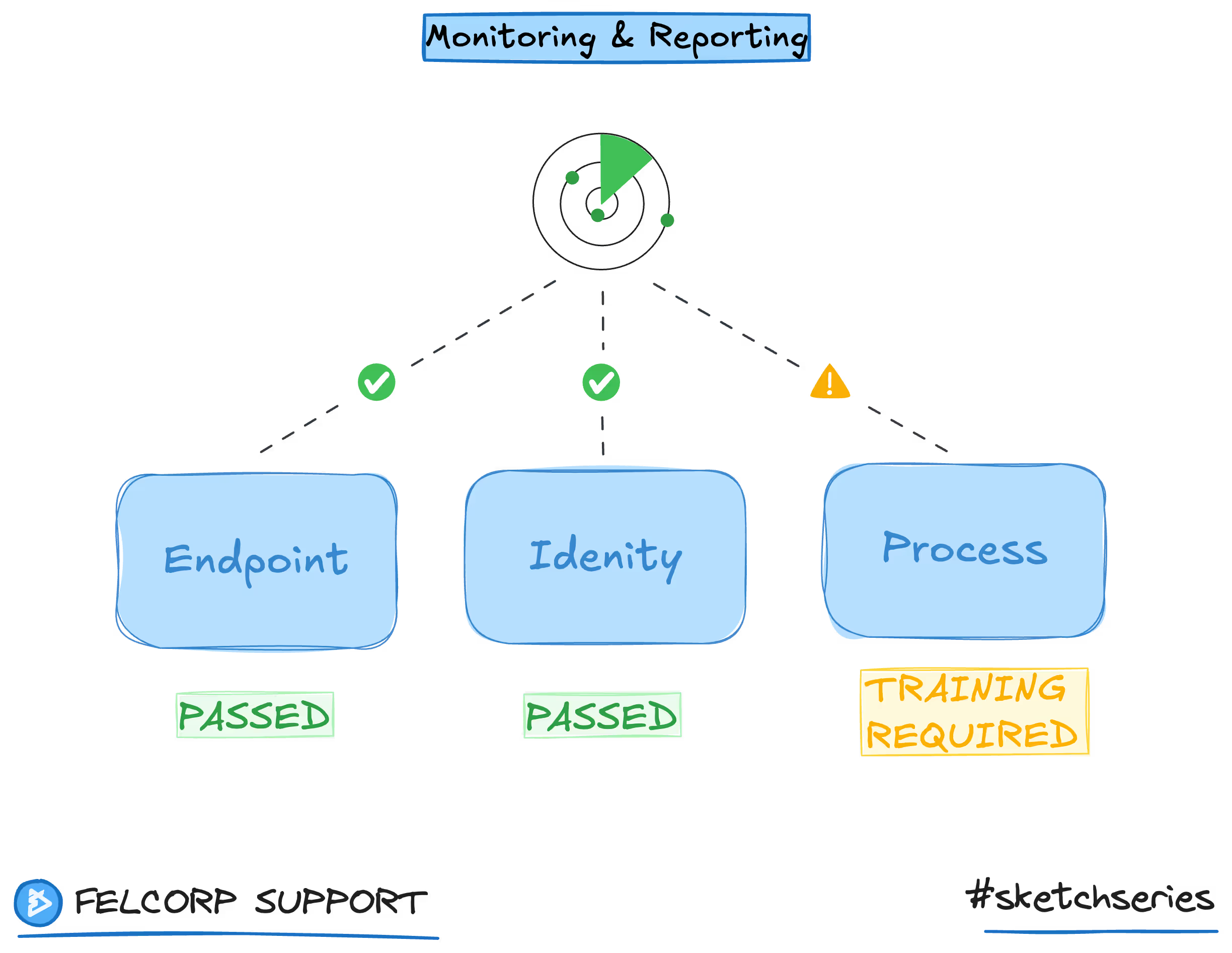
Monitoring, Detection and Response
Monitoring and reporting provide ongoing oversight of system access and activity across our operations. Monitoring activities supports early detection issues and process improvements.
Non-Disclosure Agreements
All staff are bound by confidentality and non-disclosure agreements with strict legal enforcement and corrective actions on disclosure breaches.
Secure Work Environment
Controlling how and where work is performed provides additional oversight and better protects against deliberate or accidental disclosures.
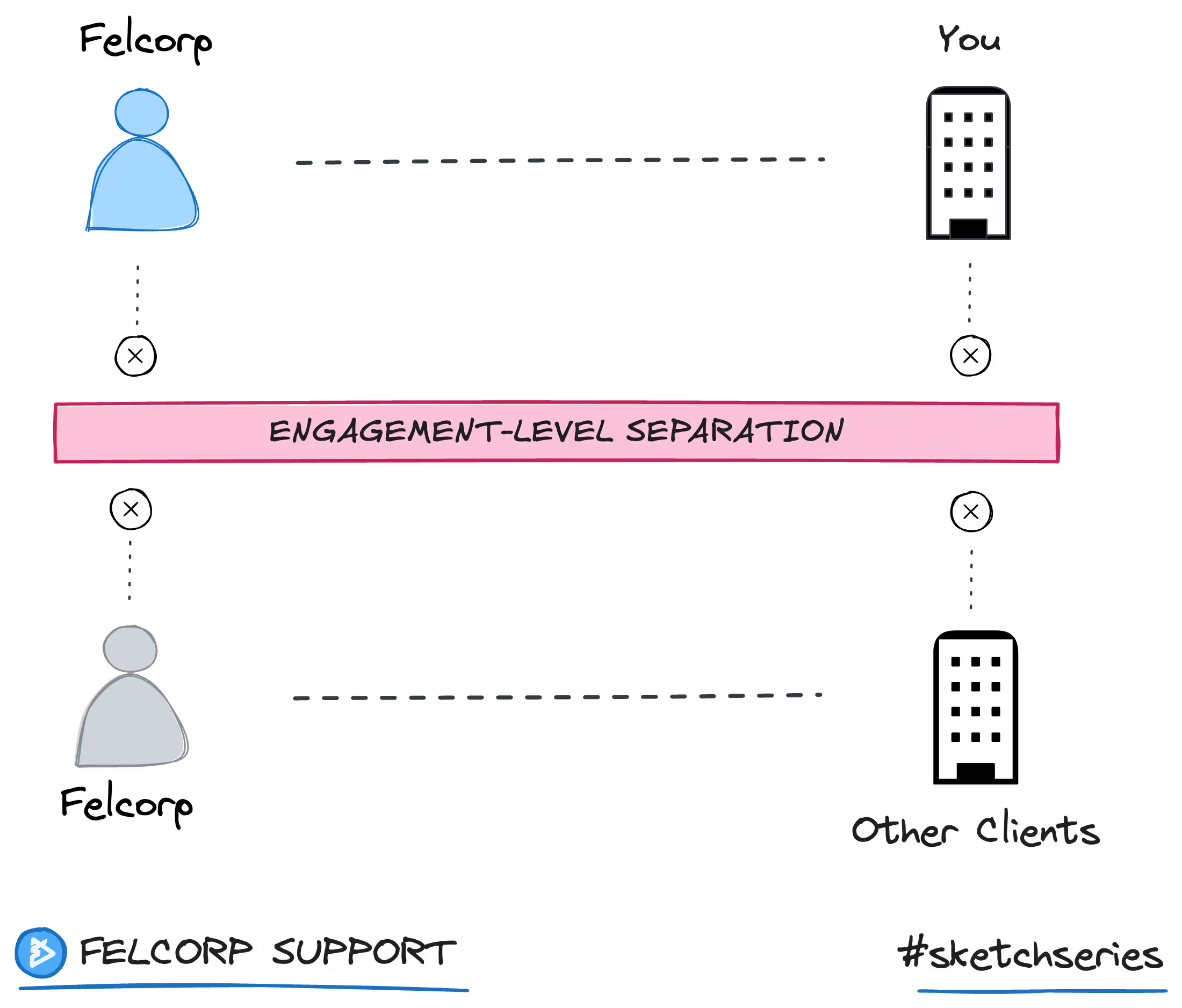
Client and Engagement-Level Separation
Ensuring information is not visible or shared with other staff and preventing cross-client disclosure between staff in their interactions.
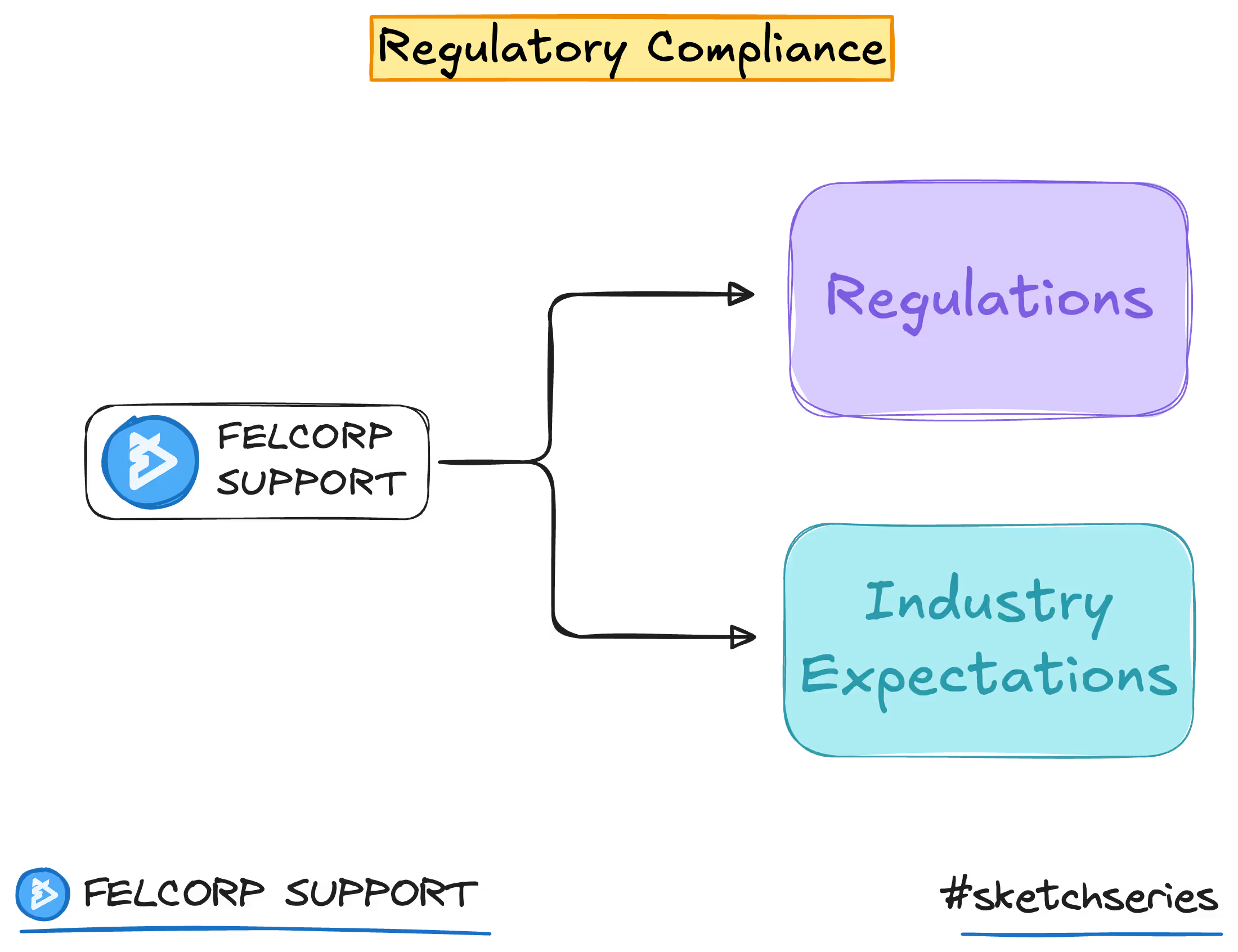
Alignment to industry regulations and expectations
Devices are locked down, continuously protected to prevent unauthorised access and malware intrusions. Security controls are enforced at the endpoint level to ensure data is protected wherever work is performed.
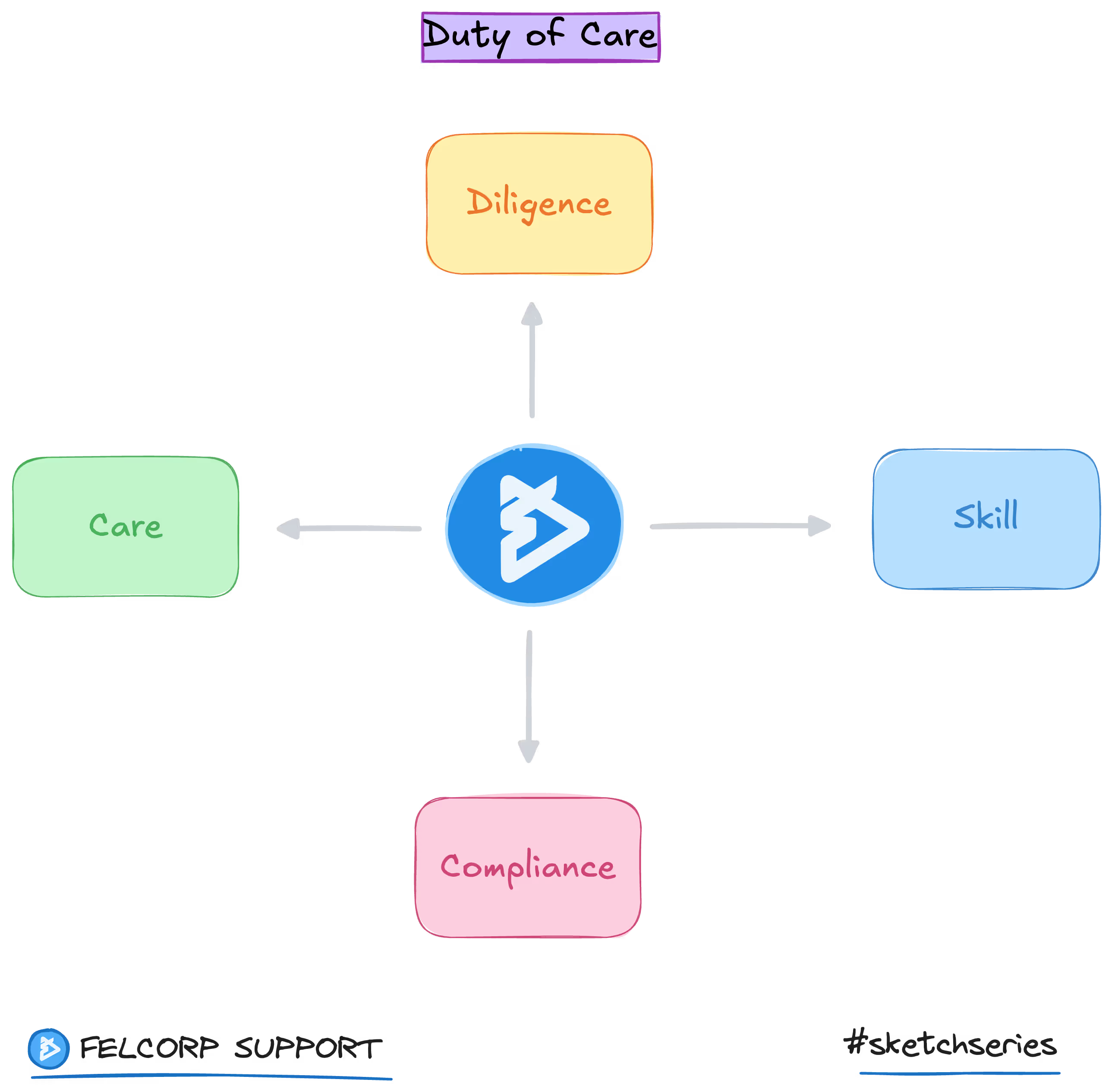
Duty of Care
Protecting client and end-customer interests with our obligation to act with due care, skill, and diligence when delivering our outsourced services.
Find more answers in our resource hub
Visit our Resource Hub for support articles that outline how our BPO service operates and how we support secure, efficient outsourcing.